Microsoft has observed cyberattacks in recent weeks targeting individuals and organizations involved in the upcoming presidential election, including unsuccessful attacks on people affiliated with both the campaigns of Trump and Biden, as detailed below. We have and will continue to protect our democracy against these attacks by notifying affected consumers of such violence, security features in our goods and services and legal and technological disruptions. The activity we announce today makes it clear that international intervention groups have, as expected, stepped up their efforts to influence the 2020 election and are consistent with what the U.S. government and others have reported. Here we also track attacks against other organizations and companies around the world that represent similar adversary behavior. We also contacted those who have been abused or compromised directly, so they can take measures to defend themselves.
What we’ve seen is consistent with past trends of attack that threaten not only politicians and campaign workers but also those they ‘re talking on key issues. These actions highlight the need for individuals and organizations active in the political process to take advantage of free and low-cost protection resources to protect themselves as we approach election day. For example, at Microsoft, we provide threat detection through AccountGuard, Microsoft 365 for Campaigns and Election Security Advisors to help protect campaigns and their volunteers. More generally, these attacks underline the continuing value of the work underway at the UN to secure cyberspace and initiatives such as the Call for Trust and Security in Cyberspace in Paris.
Stretch
Strontium is an operation group operating from Russia whose activities Microsoft has monitored on many previous occasions and has taken measures to disrupt. The Mueller report also described it as the main entity responsible for the 2016 attacks on the Democratic presidential campaign. Microsoft’s Threat Intelligence Center (MSTIC) detected a series of attacks from September 2019 through today by Strontium. Strontium is conducting programs, similar to what we witnessed in 2016, to obtain the log-in credentials of individuals or hack their accounts, possibly to assist in collecting information or disrupting operations. Many of the aims of Strontium in this movement, which has targeted more than 200 organizations in total, are directly or indirectly associated with the forthcoming U.S. election as well as with European political and policy-related organisations. Those goals include:
Others that Strontium recently targeted include entertainment, hospitality, fabrication, financial services, and physical security sectors.
For several months, Microsoft has been tracking these attacks and notifying targeted customers, but it has only recently reached a stage in our investigation where we can reliably attribute the operation to Strontium. MSTIC’s investigation found that since the 2016 election, Strontium has expanded its methods to incorporate new identification tools and new strategies to shred their operations. It has been engaged in brute force attacks and password spray in recent months , two techniques which have likely helped them to automate aspects of their operations. These credential harvesting attacks were also disguised in new ways by Strontium, running them across more than 1,000 constantly revolving IP addresses, many affiliated with the Tor anonymizing service. Between March 2020 and September 2020 we have observed thousands of attacks from Zirconium resulting in nearly 150 compromises. The goals have included two groups of people.

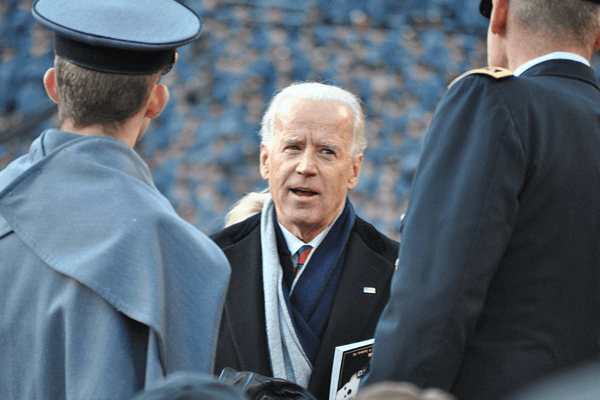
Next, the organization targets individuals closely connected with campaigns and candidates for the US presidency. For example, the Joe Biden campaign for President seems to have been targeted indirectly and unsuccessfully via non-campaign email addresses belonging to people related to the campaign. At least one influential person formerly affiliated with the Trump Administration has also been targeted by the party.
Second, the group targets influential individuals in the foreign relations sector, international affairs scholars from over 15 universities, and accounts connected to 18 international affairs and policy organizations like the Atlantic Council and the Stimson Centre. The actor then sends the linked URL to a specific account in either email text or an attachment. This is a easy way for nation-state actors to conduct verification on targeted accounts to determine if the account is legitimate or if the user is involved. The actor has run spy campaigns targeting a wide range of organizations historically tied to the Middle East region’s diplomatic, economic, or human rights interests. Prior to this, Microsoft has taken legal action against the system of Phosphorus and its plans to threaten a U.S. presidential campaign late last year. Last month, as part of our continuing efforts to disrupt Phosphorus activity, Microsoft again obtained approval from a federal court in Washington D.C. It is important that anyone participating in democratic processes around the world, directly or indirectly, be aware of these risks and take action to defend themselves in both their personal and professional capacity. We report to our customers on nation-state activity, and more generally when material to the media, regardless of the nation-state affiliation of the actor. While the political institutions targeted in these actors’ attacks are not those that manage or operate voting processes, this increased U.S. election process-related violence is of concern for the entire ecosystem. We continue to urge U.S. state and local election officials to harden their processes and plan for future assaults.
Source: blogs.microsoft.com
Carl Riedel is an experienced writer focused on using Open Source Intelligence (OSINT) to produce insightful articles. Passionate about free speech, he leverages OSINT to delve into public data, crafting stories that illuminate underreported issues, enriching public discourse with perspectives often overlooked by mainstream media.